Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,564
- Points
- 113
A Windows malware designed to steal cryptocurrencies and the contents of the clipboard installs the malicious VenomSoftX extension on users' machines. The extension works like a RAT (Remote Access Trojan), stealing victims' data and cryptocurrencies.
Information security experts have known about the existence of ViperSoftX malware since 2020, for example, Cerberus and Fortinet have already talked about it . Now the malware has been studied in more detail by Avast experts, who report that the malware has noticeably changed over time.
The company report says that since the beginning of 2022, Avast has detected and stopped 93,000 ViperSoftX attack attempts against its customers, mainly affecting users from the United States, Italy, Brazil and India. At the same time, it is known that the main distribution channel for malware is torrent files of game cracks and activators for various software.
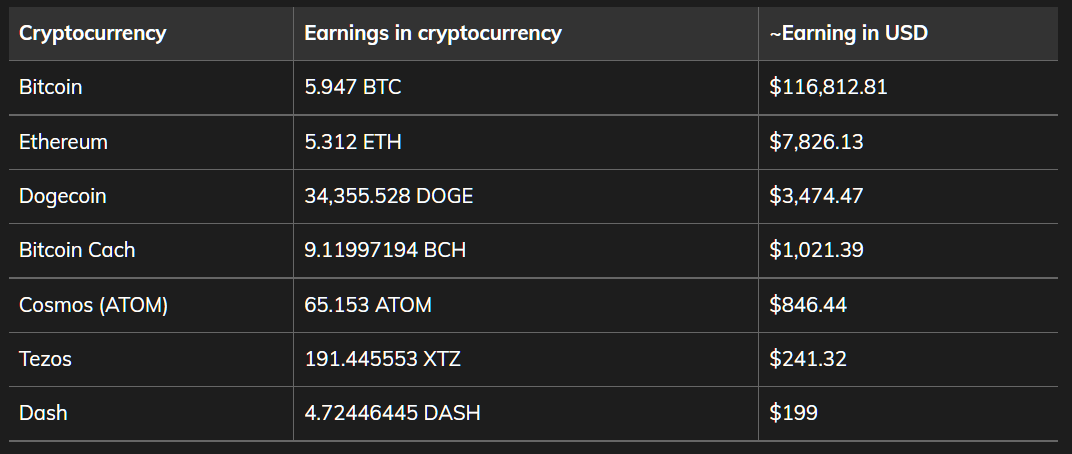
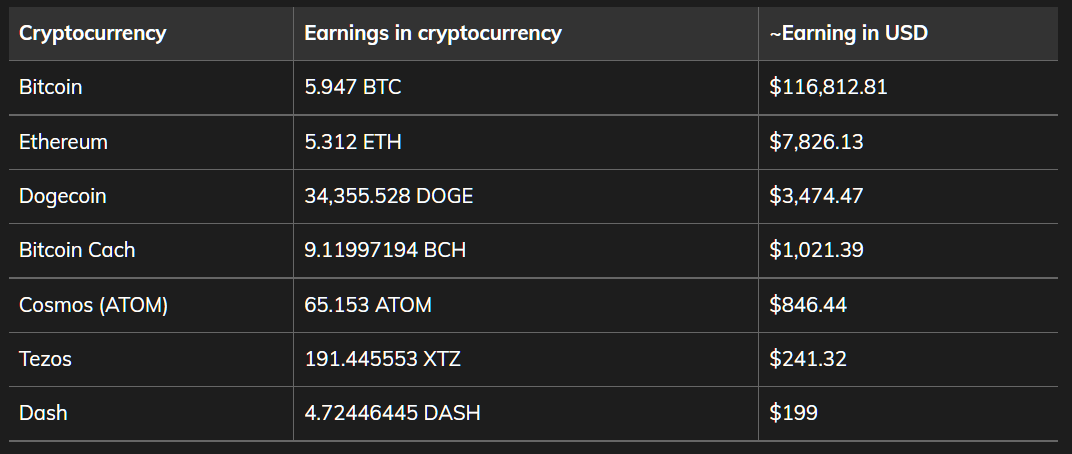
After examining the wallet addresses that are hard-coded in the ViperSoftX and VenomSoftX samples, the experts found that as of November 8, 2022, the attackers "earned" about $130,000. Moreover, the stolen cryptocurrency was obtained solely by redirecting cryptocurrency transactions on hacked devices, that is, this amount does not include profit from other activities of hackers.
The new variants of ViperSoftX themselves do not differ much from those studied earlier, that is, they can steal data from cryptocurrency wallets, execute arbitrary commands, download payloads from the control server, and so on. The main difference between the new versions of ViperSoftX is the installation of an additional malicious VenomSoftX extension in the victim's browsers (Chrome, Brave, Edge, Opera).
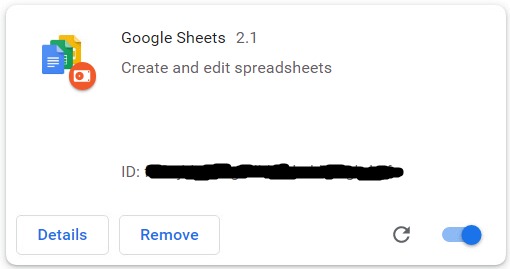
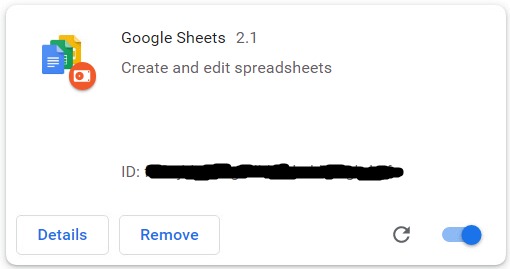
To hide from the victim, the extension masquerades as Google Sheets 2.1, allegedly created by Google, or as a certain Update Manager.
Although VenomSoftX largely duplicates the functionality of ViperSoftX (both malware targets the cryptocurrency assets of victims), the extension itself carries out the theft differently, which increases the chances of attackers to succeed.

In addition, the extension can change the HTML code on sites to detect the address of the user's cryptocurrency wallet, while manipulating elements in the background and redirecting payments to attackers.
To determine the victim's assets, the VenomSoftX extension intercepts all API requests to the aforementioned cryptocurrency services, and then sets the maximum available transaction amount, stealing all available funds.
Moreover, in the case of Blockchain.info, the extension will generally try to steal the password entered on the site.
Information security experts have known about the existence of ViperSoftX malware since 2020, for example, Cerberus and Fortinet have already talked about it . Now the malware has been studied in more detail by Avast experts, who report that the malware has noticeably changed over time.
The company report says that since the beginning of 2022, Avast has detected and stopped 93,000 ViperSoftX attack attempts against its customers, mainly affecting users from the United States, Italy, Brazil and India. At the same time, it is known that the main distribution channel for malware is torrent files of game cracks and activators for various software.
After examining the wallet addresses that are hard-coded in the ViperSoftX and VenomSoftX samples, the experts found that as of November 8, 2022, the attackers "earned" about $130,000. Moreover, the stolen cryptocurrency was obtained solely by redirecting cryptocurrency transactions on hacked devices, that is, this amount does not include profit from other activities of hackers.
The new variants of ViperSoftX themselves do not differ much from those studied earlier, that is, they can steal data from cryptocurrency wallets, execute arbitrary commands, download payloads from the control server, and so on. The main difference between the new versions of ViperSoftX is the installation of an additional malicious VenomSoftX extension in the victim's browsers (Chrome, Brave, Edge, Opera).
To hide from the victim, the extension masquerades as Google Sheets 2.1, allegedly created by Google, or as a certain Update Manager.
Although VenomSoftX largely duplicates the functionality of ViperSoftX (both malware targets the cryptocurrency assets of victims), the extension itself carries out the theft differently, which increases the chances of attackers to succeed.
In particular, VenomSoftX targets Blockchain.com, Binance, Coinbase, Gate.io and Kucoin, and the extension monitors the user's clipboard and replaces any cryptocurrency wallet addresses that fall there with the addresses of attackers.“VenomSoftX basically steals crypto by intercepting API requests for several very popular crypto exchanges that victims visit or have an account on,” the experts explain.

In addition, the extension can change the HTML code on sites to detect the address of the user's cryptocurrency wallet, while manipulating elements in the background and redirecting payments to attackers.
To determine the victim's assets, the VenomSoftX extension intercepts all API requests to the aforementioned cryptocurrency services, and then sets the maximum available transaction amount, stealing all available funds.
Moreover, in the case of Blockchain.info, the extension will generally try to steal the password entered on the site.
The researchers say it's easy to detect such fake Google Sheets: the real Google Sheets are usually installed in Chrome as an app (chrome://apps/) and not as an extension, which is fairly easy to check on said page. If the extension is present in the browser, you should remove it as soon as possible, clear the data, and probably change the passwords.“The module focuses on www.blockchain.com and tries to intercept https://blockchain.info/wallet. It also changes the getter of the password input field in order to steal the entered passwords, explains Avast. “After sending the request to the API endpoint, the wallet address is extracted from the request, associated with the password, and sent to the faucet as base64-encoded JSON via MQTT.”
