Carding
Professional
- Messages
- 2,870
- Reaction score
- 2,522
- Points
- 113
Cybercriminals use victims trust and customer focus to infect them.
Specialists of the information security company SentinelOne discovered a new malware for stealing information called MetaStealer, which is aimed at enterprises using Apple products. During the campaign, attackers impersonate customers in order to use social engineering to force victims to launch malicious payloads.
SentinelOne researchers noted that attackers actively attack business structures using macOS, using clever methods of social engineering. Hackers pose as potential customers interested in design services to force victims to run infected files.
During attacks, MetaStealer is distributed as a DMG file (Apple Disk Image Format), which is contained in a password-protected ZIP archive sent to victims. In other cases, the malware disguises itself as Adobe files or Adobe Photoshop installers. Since many macOS users trust the DMG format as a standard method of installing programs, victims do not have any suspicions about the security of the file, which the attackers took advantage of.
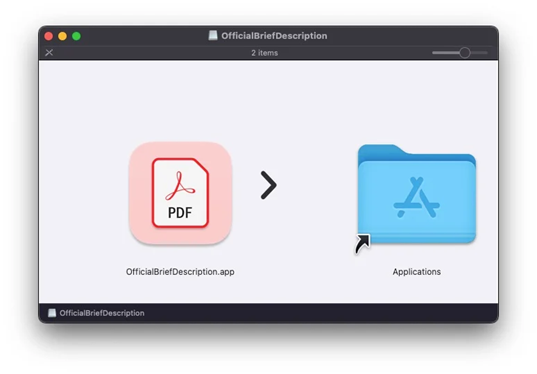
Installing a FakePDF file onmacOS
The evidence gathered so far shows that MetaStealer artifacts began appearing in nature in March 2023. The most recent sample was uploaded to VirusTotal on August 27, 2023.
SentinelOne said that such attacks on business users are unusual for malware for macOS, which is most often distributed through torrent sites or fake business software.
The obfuscated MetaStealer executable, written in Go, is capable of extracting passwords from the iCloud keychain, saved passwords, and user files. According to SentinelOne, all MetaStealer samples are optimized to run on computers with Intel processors. Such valuable data can be used to continue cybercrime activities or gain a foothold in a larger corporate network. Some versions of MetaStealer contain code aimed at compromising Telegram and Meta accounts.
It is noteworthy that several versions of MetaStealer pretend to be software for macOS TradingView — so did the Atomic Stealer infostiler, discovered in April . There are 2 options: either the same developers are behind both families of stylers, and their malware is used by different groups (due to differences in delivery mechanisms), or the stylers are developed by different hackers.
Infostiler XLoader, known for its malicious activity since 2015, in 2021 began attacking macOS systems using Java dependencies, but then disappeared from the radar for a long time. Recently, the malware returned with new features and features . In the new version, the virus is very self-contained, it is written in C and Objective-C languages and has an authentic Apple developer signature.
In August, software engineer and developer Jeff Johnson revealed a zero-day vulnerability in the macOS Ventura App Management system. According to Johnson, Apple did not take any steps to fix the problem within 10 months after the developer's initial report of the flaw.
Specialists of the information security company SentinelOne discovered a new malware for stealing information called MetaStealer, which is aimed at enterprises using Apple products. During the campaign, attackers impersonate customers in order to use social engineering to force victims to launch malicious payloads.
SentinelOne researchers noted that attackers actively attack business structures using macOS, using clever methods of social engineering. Hackers pose as potential customers interested in design services to force victims to run infected files.
During attacks, MetaStealer is distributed as a DMG file (Apple Disk Image Format), which is contained in a password-protected ZIP archive sent to victims. In other cases, the malware disguises itself as Adobe files or Adobe Photoshop installers. Since many macOS users trust the DMG format as a standard method of installing programs, victims do not have any suspicions about the security of the file, which the attackers took advantage of.
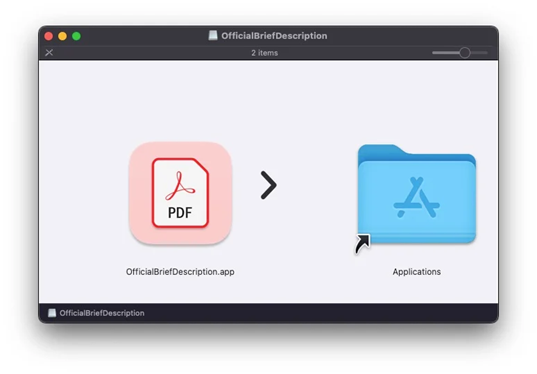
Installing a FakePDF file onmacOS
The evidence gathered so far shows that MetaStealer artifacts began appearing in nature in March 2023. The most recent sample was uploaded to VirusTotal on August 27, 2023.
SentinelOne said that such attacks on business users are unusual for malware for macOS, which is most often distributed through torrent sites or fake business software.
The obfuscated MetaStealer executable, written in Go, is capable of extracting passwords from the iCloud keychain, saved passwords, and user files. According to SentinelOne, all MetaStealer samples are optimized to run on computers with Intel processors. Such valuable data can be used to continue cybercrime activities or gain a foothold in a larger corporate network. Some versions of MetaStealer contain code aimed at compromising Telegram and Meta accounts.
It is noteworthy that several versions of MetaStealer pretend to be software for macOS TradingView — so did the Atomic Stealer infostiler, discovered in April . There are 2 options: either the same developers are behind both families of stylers, and their malware is used by different groups (due to differences in delivery mechanisms), or the stylers are developed by different hackers.
Infostiler XLoader, known for its malicious activity since 2015, in 2021 began attacking macOS systems using Java dependencies, but then disappeared from the radar for a long time. Recently, the malware returned with new features and features . In the new version, the virus is very self-contained, it is written in C and Objective-C languages and has an authentic Apple developer signature.
In August, software engineer and developer Jeff Johnson revealed a zero-day vulnerability in the macOS Ventura App Management system. According to Johnson, Apple did not take any steps to fix the problem within 10 months after the developer's initial report of the flaw.
