Brute force is a method of hacking accounts by guessing passwords for them. The term is derived from the English phrase, which means "brute force". The essence of the approach lies in sequential automated enumeration of all possible combinations of characters in order to find the correct one sooner or later. From this point of view, password search can be viewed as a mathematical problem, the solution of which is found with a sufficiently large number of attempts. The brute-force software generates password variations and checks each one. From the point of view of mathematics, it is always possible to solve a problem in this way, but the time spent on searches does not in all cases justify the goal, since the field of finding solutions is huge.
Brute force is one of the most popular methods to crack passwords for accounts of online banks, payment systems and other websites. However, as the password length grows, this method becomes inconvenient, since the time it takes to search through all possible options grows. It can also be used to check the cryptographic strength of the password.
Brute force is also called the exhaustion method, since the correct combination is identified by analyzing all possible options and discarding each inappropriate combination.
Classification and methods of performing a brute force attack
There are several types of brute force attacks:
Brute force targets
Brute force allows you to seize access to accounts on social networks or online games, which can lead to the loss of confidential information, digital currencies, achievements, and the falling of correspondence into the wrong hands. Accounts can send spam, extortion and other illegal actions. Having taken possession of a large number of accounts, a hacker can exchange or sell them.
Obtaining data to enter payment systems threatens users with the loss of money and even the acquisition of debts, since the attacker can freely dispose of finances, transfer money, and issue a loan.
Using brute force to brute-force passwords to websites opens access to customer databases, email addresses, the use of the site in order to spread malware, send spam, etc.
Having obtained an entry point to a remote computer system using brute-force passwords, an attacker can perform various criminal actions on behalf of the user, as well as use his personal data for the purpose of blackmail, extortion, and steal secret information and money.
The objects of influence of brute force are not only computers and accounts of ordinary Internet users, but also sites, servers, workstations of commercial and banking structures, and various organizations.
Source of threat
The brute-force method is used by cyber-bullies to hack the game, mail, social media account. Usually their goal is to cause trouble for other people, test their skills, read personal correspondence.
Cybercriminals write hacking programs themselves or use the work of their “colleagues”. For enumeration, powerful computer systems can be used, including previously hacked or rented ones. In the hands of attackers, brute-force is a means of extracting personal gain from gaining access to credentials.
Also, as already noted, brute-force can be used to check the cryptographic strength of passwords.
Risk analysis
The risks of using brute force depend on the number of objects targeted by attacks and the intentions of the attacker. Every year, new technologies appear that can be used for both good and criminal purposes. So, a few years ago at the DEF CON conference, the public was presented with WASP - a drone that can collect statistics on home Wi-Fi networks. A powerful computer on board the device, among other functions, had the ability to automatically crack passwords using brute force.
Recently, a new botnet was spotted infiltrating computer systems by brute-force SSH passwords. The defenses commonly used against brute-force attacks do not work. How, in this case, to increase the level of security, you can learn from our article.
Problems with hacking through brute force can be avoided if:
Brute force is one of the most popular methods to crack passwords for accounts of online banks, payment systems and other websites. However, as the password length grows, this method becomes inconvenient, since the time it takes to search through all possible options grows. It can also be used to check the cryptographic strength of the password.
Brute force is also called the exhaustion method, since the correct combination is identified by analyzing all possible options and discarding each inappropriate combination.
Classification and methods of performing a brute force attack
There are several types of brute force attacks:
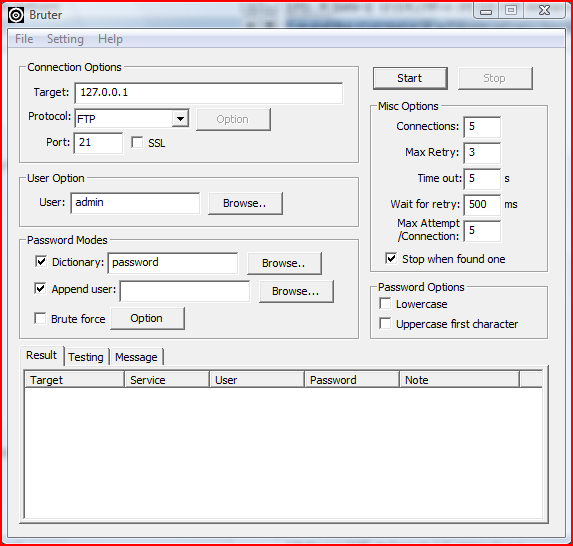
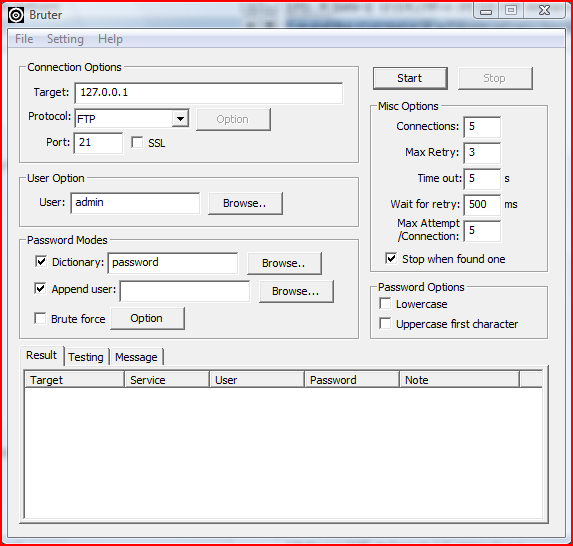
- Personal hacking. In this case, brute force is aimed at gaining access to the personal data of a specific user: social media accounts, mail, website. When communicating over the Internet, including using fraudulent schemes, the attacker tries to find out the login, personal information and other information that will be needed to guess the password. Next, the cracker writes in a special program the address of the resource to which access is needed, the account login, connects the dictionary and selects the password. If the user's password is based on personal information and consists of a small number of characters, then the attacker's attempt can be successful even in a short time.
- "Brute-check". This kind of brute-force means hunting for large numbers of passwords. Accordingly, the goal is to take possession of the data of not one user, but of many different accounts on several web resources. A database of logins and passwords of some mail services is connected to the hacker program, as well as a proxy list to disguise the site, preventing web mail services from detecting the attack. When registering on the site, on a social network or in the game, the user fills in the field with his email address, which receives the data to log into the corresponding account. The brute force options prescribe a list of site names or other keywords by which the program will search in mailboxes for these letters with logins and passwords, extract and copy information into a separate file. This way a cybercriminal obtains hundreds of passwords and can use them for any purpose.
- Remote hacking of the operating system of a computer device. Brute force in combination with other hacking tools is used to gain access to a remote PC. This kind of hacking begins with finding suitable networks for the attack. User addresses are obtained by special programs or taken from databases. Brute force dictionaries and lists of IP addresses are entered in the brute force settings. If the password is successfully brute-force, the victim's machine IP address and login data are saved, which are then used by the attacker - for example, in order to fully control the PC through the Radmin utility or another similar program.
Brute force targets
Brute force allows you to seize access to accounts on social networks or online games, which can lead to the loss of confidential information, digital currencies, achievements, and the falling of correspondence into the wrong hands. Accounts can send spam, extortion and other illegal actions. Having taken possession of a large number of accounts, a hacker can exchange or sell them.
Obtaining data to enter payment systems threatens users with the loss of money and even the acquisition of debts, since the attacker can freely dispose of finances, transfer money, and issue a loan.
Using brute force to brute-force passwords to websites opens access to customer databases, email addresses, the use of the site in order to spread malware, send spam, etc.
Having obtained an entry point to a remote computer system using brute-force passwords, an attacker can perform various criminal actions on behalf of the user, as well as use his personal data for the purpose of blackmail, extortion, and steal secret information and money.
The objects of influence of brute force are not only computers and accounts of ordinary Internet users, but also sites, servers, workstations of commercial and banking structures, and various organizations.
Source of threat
The brute-force method is used by cyber-bullies to hack the game, mail, social media account. Usually their goal is to cause trouble for other people, test their skills, read personal correspondence.
Cybercriminals write hacking programs themselves or use the work of their “colleagues”. For enumeration, powerful computer systems can be used, including previously hacked or rented ones. In the hands of attackers, brute-force is a means of extracting personal gain from gaining access to credentials.
Also, as already noted, brute-force can be used to check the cryptographic strength of passwords.
Risk analysis
The risks of using brute force depend on the number of objects targeted by attacks and the intentions of the attacker. Every year, new technologies appear that can be used for both good and criminal purposes. So, a few years ago at the DEF CON conference, the public was presented with WASP - a drone that can collect statistics on home Wi-Fi networks. A powerful computer on board the device, among other functions, had the ability to automatically crack passwords using brute force.
Recently, a new botnet was spotted infiltrating computer systems by brute-force SSH passwords. The defenses commonly used against brute-force attacks do not work. How, in this case, to increase the level of security, you can learn from our article.
Problems with hacking through brute force can be avoided if:
- create a long password from letters, numbers and special characters,
- do not use personal information or any login elements in the password,
- create unique passwords for all accounts,
- regularly, about once a month, change passwords,
- on websites to protect the login from multiple data entry attempts.
