Lord777
Professional
- Messages
- 2,576
- Reaction score
- 1,564
- Points
- 113
Reputable experts from "High Sierra Cyber Security" turned out to be nothing more than a fake, with other people's photos and data.
A malicious campaign recently discovered by VulnCheck researchers once again proves that attackers are constantly inventing new strategies in an attempt to fool their victims and achieve what they want.
Last month, fake accounts began appearing on GitHub and Twitter*, imitating security researchers from various large companies. On behalf of white hackers united "under the roof "of the fictitious company" High Sierra Cyber Security", attackers publish fake PoC exploits for zero-day vulnerabilities that, ironically, infect Windows and Linux computers with malware.
Hackers accounts look quite legitimate, as they imitate real researchers from various cybersecurity companies, using their names and photos.
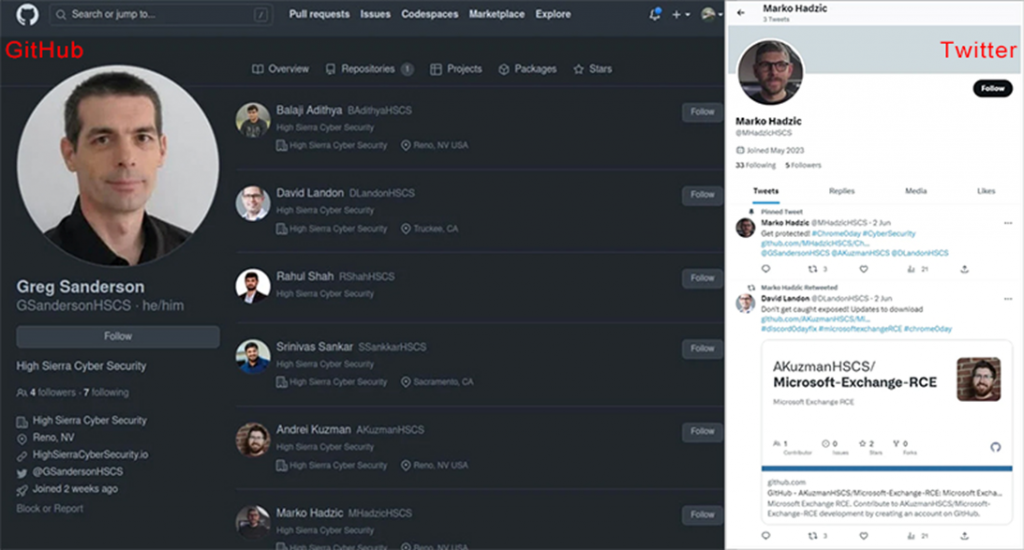
Fake accounts that pretend to be real specialists
According to the researchers, attackers mainly publish exploits for zero-day vulnerabilities in popular software such as Chrome, Discord, Signal, WhatsApp and Microsoft Exchange. In all cases, malicious repositories contain a Python script that acts as a malware loader for Linux and Windows systems.
The script downloads a ZIP archive from an external URL to the victim's computer, depending on its operating system: Linux users download " cveslinux.zip", and Windows users get "cveswindows.zip". Malware is saved in the %Temp% folder for Windows or /home/<username>/.local/share for Linux, extracted, and run.
VulnCheck reports that the executable file for Windows is detected by more than 60% of antivirus engines on VirusTotal. When as an executable file for Linux is much more secretive and is detected by only three scanners.
The scale of distribution and the number of victims of this campaign is still unclear, but VulnCheck notes that attackers are quite persistent and regularly create new accounts and repositories when existing ones are deleted due to complaints.
Cybersecurity researchers and enthusiasts should be extremely careful when downloading scripts from unknown repositories, as the owner of one of these repositories may well be scammers.
The North Korean hacker group Lazarus conducted a similar campaign in early 2021. Back then, digital bandits also created fake profiles of vulnerability researchers on social networks in order to attack researchers with malware disguised as PoC exploits.
By infecting the devices of cybersecurity researchers, attackers can gain access to unpublished vulnerability research that can later be used in their own attacks. Or even better, commit a ransomware attack, after which the company's reputation will be permanently damaged. After all, what kind of cybersecurity company is this that didn't protect itself from an attack?
When uploading code from GitHub, you should carefully check it for malicious behavior. In the case discussed above, the download and execution of malware is visible to the naked eye when examining the code, but this may not always be the case, especially if attackers deliberately obfuscate malicious code. That is why the vigilance of researchers against the background of such attacks should be maximized.
A malicious campaign recently discovered by VulnCheck researchers once again proves that attackers are constantly inventing new strategies in an attempt to fool their victims and achieve what they want.
Last month, fake accounts began appearing on GitHub and Twitter*, imitating security researchers from various large companies. On behalf of white hackers united "under the roof "of the fictitious company" High Sierra Cyber Security", attackers publish fake PoC exploits for zero-day vulnerabilities that, ironically, infect Windows and Linux computers with malware.
Hackers accounts look quite legitimate, as they imitate real researchers from various cybersecurity companies, using their names and photos.
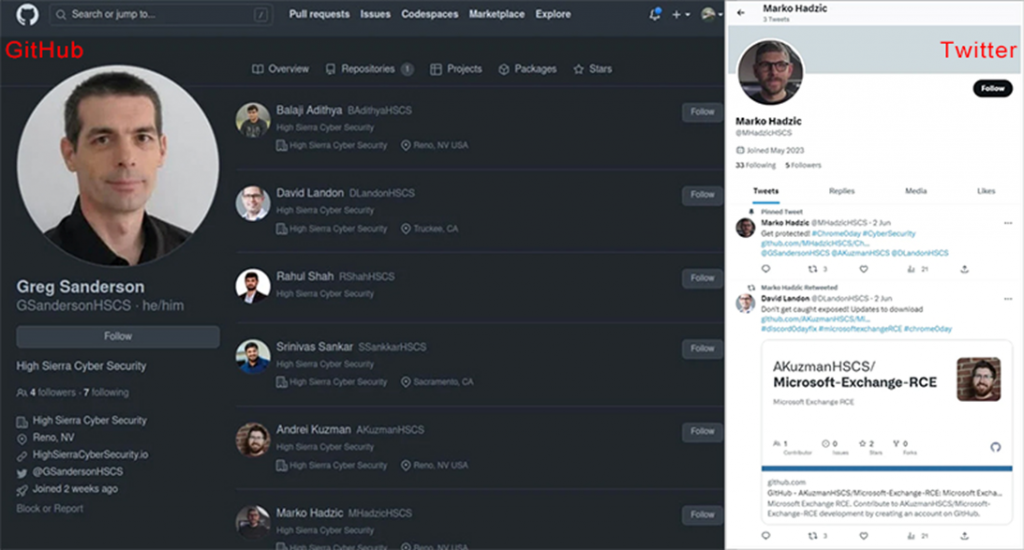
Fake accounts that pretend to be real specialists
According to the researchers, attackers mainly publish exploits for zero-day vulnerabilities in popular software such as Chrome, Discord, Signal, WhatsApp and Microsoft Exchange. In all cases, malicious repositories contain a Python script that acts as a malware loader for Linux and Windows systems.
The script downloads a ZIP archive from an external URL to the victim's computer, depending on its operating system: Linux users download " cveslinux.zip", and Windows users get "cveswindows.zip". Malware is saved in the %Temp% folder for Windows or /home/<username>/.local/share for Linux, extracted, and run.
VulnCheck reports that the executable file for Windows is detected by more than 60% of antivirus engines on VirusTotal. When as an executable file for Linux is much more secretive and is detected by only three scanners.
The scale of distribution and the number of victims of this campaign is still unclear, but VulnCheck notes that attackers are quite persistent and regularly create new accounts and repositories when existing ones are deleted due to complaints.
Cybersecurity researchers and enthusiasts should be extremely careful when downloading scripts from unknown repositories, as the owner of one of these repositories may well be scammers.
The North Korean hacker group Lazarus conducted a similar campaign in early 2021. Back then, digital bandits also created fake profiles of vulnerability researchers on social networks in order to attack researchers with malware disguised as PoC exploits.
By infecting the devices of cybersecurity researchers, attackers can gain access to unpublished vulnerability research that can later be used in their own attacks. Or even better, commit a ransomware attack, after which the company's reputation will be permanently damaged. After all, what kind of cybersecurity company is this that didn't protect itself from an attack?
When uploading code from GitHub, you should carefully check it for malicious behavior. In the case discussed above, the download and execution of malware is visible to the naked eye when examining the code, but this may not always be the case, especially if attackers deliberately obfuscate malicious code. That is why the vigilance of researchers against the background of such attacks should be maximized.
