Carding Forum
Professional
- Messages
- 2,788
- Reaction score
- 1,322
- Points
- 113
Cloudflare discloses statistics on the use of exploits.
Cyberattacks based on PoC exploits start happening at an incredible rate-sometimes as little as 22 minutes after the PoC is published. A new report from Cloudflare, covering the period from May 2023 to March 2024, tells about the trends of attackers.
Cloudflare, which processes an average of 57 million HTTP requests per second, is seeing an increase in CVE vulnerability scanning activity, accompanied by attempts to inject commands and use PoC exploits. During the study period, the most frequently attacked vulnerabilities were:
Particularly notable is CVE-2024-27198 (CVSS score: 9.8), an authentication bypass vulnerability in JetBrains TeamCity. Cloudflare recorded a case where an attacker used a PoC exploit 22 minutes after it was published, leaving no time for defenders to respond.

The speed of exploiting the CVE-2024-27198 vulnerability in TeamCity
The only way to combat this rate of attacks, according to Cloudflare, is to use artificial intelligence to quickly develop effective detection rules. The report explains that the speed of exploiting disclosed vulnerabilities often exceeds the speed of creating rules for firewalls or developing and deploying patches to mitigate attacks.
Individual attackers specialize in specific CVE categories and products, which allows them to quickly take advantage of new flaws. This focus leads to the fact that even experienced security teams do not always have time to counteract threats.
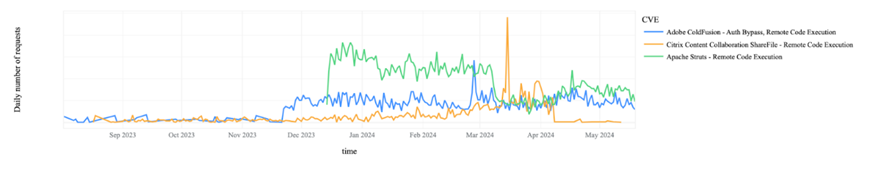
Attempts to exploit RCE vulnerabilities in specific products
There is also a significant increase in DDoS attack traffic, which accounts for 6.8% of the total Internet traffic. This is a significant increase compared to the 6% recorded between 2022 and 2023. During large global attacks, the share of malicious traffic can reach 12% of all HTTP traffic.
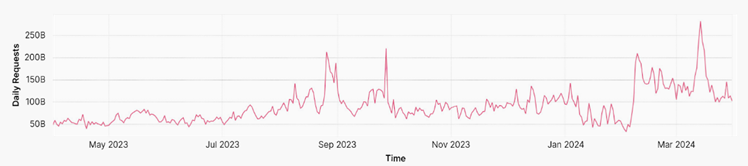
Volume of HTTP DDoS attacks over time
In the first quarter of 2024, an average of 209 billion cyber threats were blocked daily, an increase of 86.6% compared to the same period last year. This growth indicates a significant increase in the number of cyber attacks and the complexity of their prevention tasks.
In its report, Cloudflare also provides additional recommendations for defenders and deeper insights on the collected statistics. The full report is available for download.
Source
Cyberattacks based on PoC exploits start happening at an incredible rate-sometimes as little as 22 minutes after the PoC is published. A new report from Cloudflare, covering the period from May 2023 to March 2024, tells about the trends of attackers.
Cloudflare, which processes an average of 57 million HTTP requests per second, is seeing an increase in CVE vulnerability scanning activity, accompanied by attempts to inject commands and use PoC exploits. During the study period, the most frequently attacked vulnerabilities were:
- CVE-2023-50164 (CVSS score: 9.8) and CVE-2022-33891 (CVSS score: 8.8) in Apache products;
- CVE-2023-29298 (CVSS score: 7.5), CVE-2023-38203 (CVSS score: 9.8) and CVE-2023-26360 (CVSS score: 9.8) in Coldfusion;
- CVE-2023-35082 (CVSS score: 9.8) in Ivanti EPMM (formerly MobileIron).
Particularly notable is CVE-2024-27198 (CVSS score: 9.8), an authentication bypass vulnerability in JetBrains TeamCity. Cloudflare recorded a case where an attacker used a PoC exploit 22 minutes after it was published, leaving no time for defenders to respond.

The speed of exploiting the CVE-2024-27198 vulnerability in TeamCity
The only way to combat this rate of attacks, according to Cloudflare, is to use artificial intelligence to quickly develop effective detection rules. The report explains that the speed of exploiting disclosed vulnerabilities often exceeds the speed of creating rules for firewalls or developing and deploying patches to mitigate attacks.
Individual attackers specialize in specific CVE categories and products, which allows them to quickly take advantage of new flaws. This focus leads to the fact that even experienced security teams do not always have time to counteract threats.
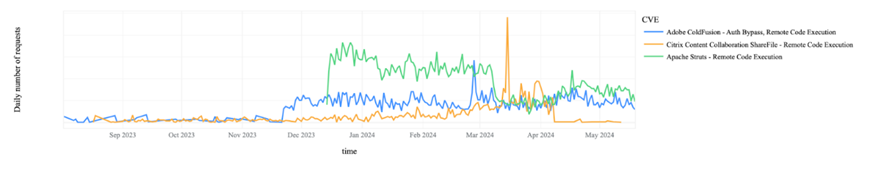
Attempts to exploit RCE vulnerabilities in specific products
There is also a significant increase in DDoS attack traffic, which accounts for 6.8% of the total Internet traffic. This is a significant increase compared to the 6% recorded between 2022 and 2023. During large global attacks, the share of malicious traffic can reach 12% of all HTTP traffic.
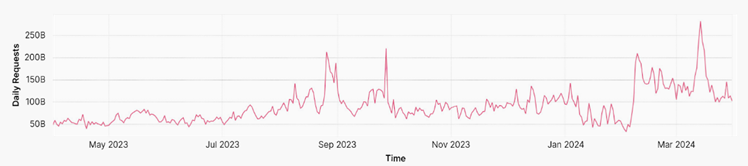
Volume of HTTP DDoS attacks over time
In the first quarter of 2024, an average of 209 billion cyber threats were blocked daily, an increase of 86.6% compared to the same period last year. This growth indicates a significant increase in the number of cyber attacks and the complexity of their prevention tasks.
In its report, Cloudflare also provides additional recommendations for defenders and deeper insights on the collected statistics. The full report is available for download.
Source

