Teacher
Professional
- Messages
- 2,669
- Reaction score
- 819
- Points
- 113
Hello, running in the shadows! Hello, random carders. If someone still thinks that cyber attacks are a concept from science fiction novels and in no way applies to real life, then they are really mistaken. In fact, even behind the guise of a modest programmer, a formidable hacker can hide, who only dreams of hacking a couple of sites. Moreover, often the sites of world-famous companies are victims of criminal talent.
Go:
1. "Nuclear attack via payphone..."
Hacker Kevin Mitnick.
Hacker Kevin Mitnick spent 8 months in solitary confinement because "law enforcement authorities informed the judge that he could somehow connect to a NORAD modem via a payphone from prison." The main charge was that he could give instructions to launch nuclear missiles through the phone.
2. Marijuana

If there is no grass, there is no public service.
According to the director of the FBI, the Federal Bureau of Investigation can not fill all vacancies in the fight against cybercrime. The reason is ridiculously paradoxical - many of the country's best computer programmers and hackers love marijuana and are therefore reluctant to cooperate with the authorities.
3. "We have no barriers..."

Hacked the jail's mainframe.
Funny and sinful. An American hacker who was jailed for five years for hacking websites went to prison for IT courses. During class, he successfully hacked into the prison's mainframe.
4. Envy and incompetence

Online poker and "hacking federal networks".
Two Americans tried to sue for "hacking federal networks", because they used a bug in online poker and won half a million dollars. Their lawyer said that "these guys just pressed a certain sequence of buttons that they had a legal right to press," and ... won the case.
5. Intelligence Agencies and Lenovo Computers

Lenovo Computers is partly owned by the Chinese government.
Lenovo computers are delivered with pre-installed secret access by state intelligence agencies. As a result, MI6, the CIA and other spy agencies banned their use.
6. Delayed revenge
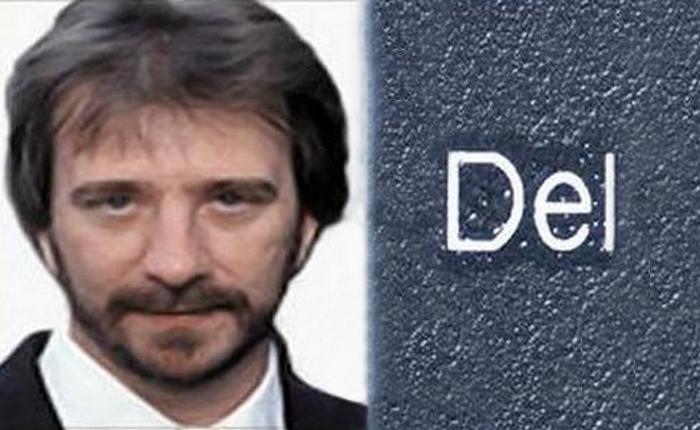
Timothy Lloyd removed the main operating software.
Timothy Lloyd, who worked for Omega Engineering Corporation for 11 years, launched a "time bomb" in the company's computer systems after his dismissal in 1996. His program removed the firm's core operating software two weeks after he was fired, causing the company to lose more than $ 10 million and lay off 80 employees.
7. "Father's setup"

Fragment of the "Fortune 500" list.
During the hacking of another Fortune 500 company, the father took away the keyboard from 16-year-old Sean Parker, angry that his son was constantly sitting at the computer. As a result, Sean was unable to log out, the FBI agents found out his IP address and arrested the teenager.
8. There is no such crime!
There is no such law...
The first person to be charged with computer hacking was never jailed. At that time, there was simply no law providing for a criminal offense for such a thing.
9. Hacking the "peaceful atom"

In 2007, an IBM engineer was able to gain full control of an American nuclear power plant. He was able to hack it quite easily over the Internet.
10. The first cybercriminal
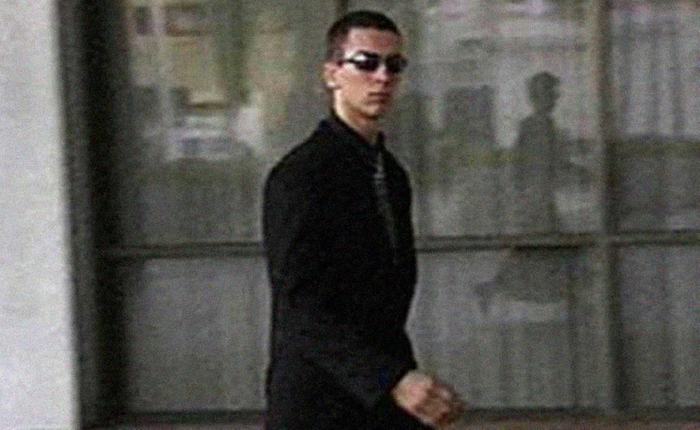
15-year-old Jonathan James.
A 15-year-old teenager named Jonathan James once hacked into the NASA website, after which the agency's computers failed for 21 days. James was subject to federal prosecution after hacking the United States Department of Computer Security and became the first minor to be jailed for cybercrime in the United States.
11. Mobile phone hacking

Millie Dowler.
Journalists hacked the mobile phone of Millie Dowler, a 13-year-old girl who was abducted and killed in 2002. After they read the text message and listened to her voice message sent to family, friends and the police, all hope that the girl was still alive disappeared.
12. Natural hacking of the Matrix
Still from the movie "The Matrix".
Today, the film "The Matrix" has become a cult film. However, few people know that the hacking of the computer during this period was carried out using real software.
13. $ 1 billion from 100 banks

"Happy Hacker Year".
In the 90s, there was a group of hackers who clearly showed the US Congress that they could shut down the entire Internet in 30 minutes. And in 2015, hackers managed to" steal " about $ 1 billion from more than 100 banks.
14. "The Victorian Internet"
The forerunner of the Internet.
The 19th-century telegraph network has been dubbed the "Victorian Internet"by some. At that time, people used it for hacking, dating, fraud, and spam.
15. Time distortions of satellites

A GPS satellite.
GPS satellites have been programmed to use time distortions in their signals. This was only abolished by a presidential decree in 2000.
That's it, cyberstalkers. As you can see, everything is in our hands - and the opportunity to get more money and the opportunity to sit down for a longer time, if you sleep. So, fuck off and don't fall down.
novate.ru
Go:
1. "Nuclear attack via payphone..."
Hacker Kevin Mitnick.
Hacker Kevin Mitnick spent 8 months in solitary confinement because "law enforcement authorities informed the judge that he could somehow connect to a NORAD modem via a payphone from prison." The main charge was that he could give instructions to launch nuclear missiles through the phone.
2. Marijuana

If there is no grass, there is no public service.
According to the director of the FBI, the Federal Bureau of Investigation can not fill all vacancies in the fight against cybercrime. The reason is ridiculously paradoxical - many of the country's best computer programmers and hackers love marijuana and are therefore reluctant to cooperate with the authorities.
3. "We have no barriers..."

Hacked the jail's mainframe.
Funny and sinful. An American hacker who was jailed for five years for hacking websites went to prison for IT courses. During class, he successfully hacked into the prison's mainframe.
4. Envy and incompetence

Online poker and "hacking federal networks".
Two Americans tried to sue for "hacking federal networks", because they used a bug in online poker and won half a million dollars. Their lawyer said that "these guys just pressed a certain sequence of buttons that they had a legal right to press," and ... won the case.
5. Intelligence Agencies and Lenovo Computers

Lenovo Computers is partly owned by the Chinese government.
Lenovo computers are delivered with pre-installed secret access by state intelligence agencies. As a result, MI6, the CIA and other spy agencies banned their use.
6. Delayed revenge
Timothy Lloyd removed the main operating software.
Timothy Lloyd, who worked for Omega Engineering Corporation for 11 years, launched a "time bomb" in the company's computer systems after his dismissal in 1996. His program removed the firm's core operating software two weeks after he was fired, causing the company to lose more than $ 10 million and lay off 80 employees.
7. "Father's setup"

Fragment of the "Fortune 500" list.
During the hacking of another Fortune 500 company, the father took away the keyboard from 16-year-old Sean Parker, angry that his son was constantly sitting at the computer. As a result, Sean was unable to log out, the FBI agents found out his IP address and arrested the teenager.
8. There is no such crime!
There is no such law...
The first person to be charged with computer hacking was never jailed. At that time, there was simply no law providing for a criminal offense for such a thing.
9. Hacking the "peaceful atom"

In 2007, an IBM engineer was able to gain full control of an American nuclear power plant. He was able to hack it quite easily over the Internet.
10. The first cybercriminal
15-year-old Jonathan James.
A 15-year-old teenager named Jonathan James once hacked into the NASA website, after which the agency's computers failed for 21 days. James was subject to federal prosecution after hacking the United States Department of Computer Security and became the first minor to be jailed for cybercrime in the United States.
11. Mobile phone hacking

Millie Dowler.
Journalists hacked the mobile phone of Millie Dowler, a 13-year-old girl who was abducted and killed in 2002. After they read the text message and listened to her voice message sent to family, friends and the police, all hope that the girl was still alive disappeared.
12. Natural hacking of the Matrix
Still from the movie "The Matrix".
Today, the film "The Matrix" has become a cult film. However, few people know that the hacking of the computer during this period was carried out using real software.
13. $ 1 billion from 100 banks

"Happy Hacker Year".
In the 90s, there was a group of hackers who clearly showed the US Congress that they could shut down the entire Internet in 30 minutes. And in 2015, hackers managed to" steal " about $ 1 billion from more than 100 banks.
14. "The Victorian Internet"
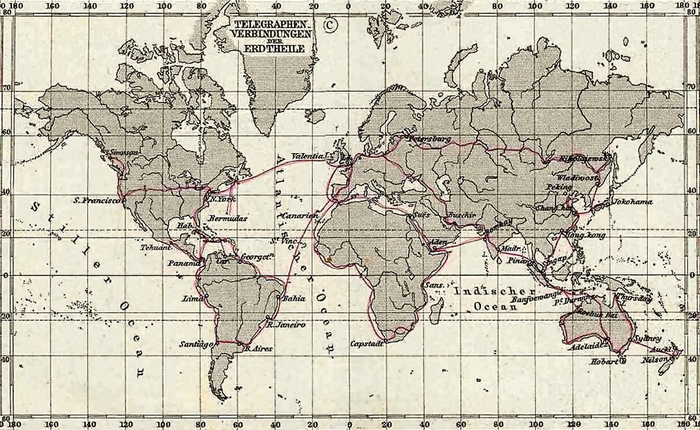
The forerunner of the Internet.
The 19th-century telegraph network has been dubbed the "Victorian Internet"by some. At that time, people used it for hacking, dating, fraud, and spam.
15. Time distortions of satellites

A GPS satellite.
GPS satellites have been programmed to use time distortions in their signals. This was only abolished by a presidential decree in 2000.
That's it, cyberstalkers. As you can see, everything is in our hands - and the opportunity to get more money and the opportunity to sit down for a longer time, if you sleep. So, fuck off and don't fall down.
novate.ru

